- [ Cybersecurity ]
Securing Your Enterprise Assets
- [ Scale & Velocity ]
Quantifiable Resilience: American Security Standards Backed By Real-Time Intelligence And Technical Superiority.



50+ Specialists
Threat Neutralization
Trust Frameworks




10M+ Users
Compliance Ready
- [ The Strategic Core ]
Threat Hunting Built On A Foundation Of Intelligence
Passive security is no longer enough in an AI-driven threat landscape. Our process begins with a “Vulnerability Mapping Phase” in our Texas studio, where we simulate sophisticated attacks to identify the invisible gaps in your current infrastructure. We don’t wait for a breach; we hunt for the potential of one, ensuring your digital moat is unbreachable from every angle, regardless of where your offices are located.
- Penetration Testing
- End-Point Protection
- Cloud Security
- Disaster Recovery
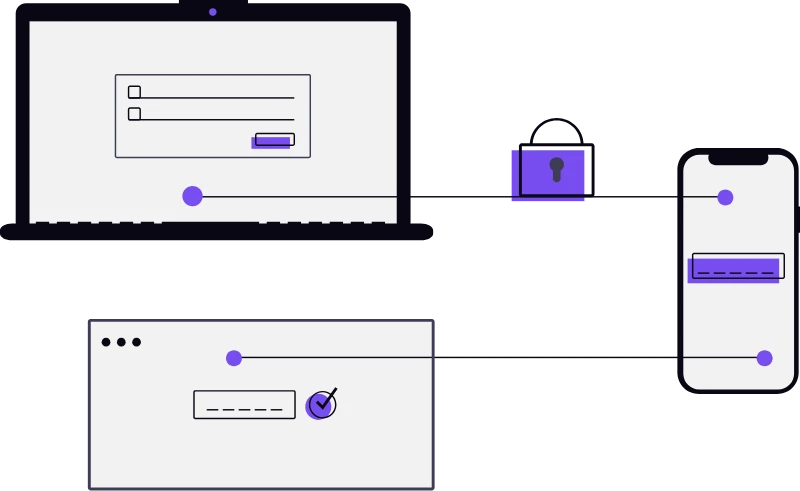
Autonomous Threat Detection
Military-Grade Encryption
Identity & Access Management
- [ The AI Advantage ]
Outpace Sophisticated Global Cyber Attacks.
Predictive Patching
AI that identifies and fixes software vulnerabilities automatically.
Anomaly Detection
Immediate alerts for any behavior that deviates from the US baseline.
SecOps Automation
Reducing human error through automated, high-velocity security workflows.
Global Threat Intelligence
Real-time data feeds from top-tier US and international security agencies.
Future-Proof Defense
The next generation of cyber-attacks will be powered by AI; therefore, your defense must be as well. At Techronics, we integrate custom-trained neural models that learn the unique "pulse" of your business operations. This allows our systems to distinguish between legitimate high-volume activity and a coordinated "Brute Force" or "DDoS" attack with absolute certainty, protecting your US operations 24/7.

- [ FAQs ]
Frequently Asked Questions Regarding Our Cybersecurity Protocols.
Is your security team based in the United States?
Yes. Our core security architects and incident response leads operate directly out of our Frisco, Texas headquarters, ensuring compliance with US security regulations and immediate domestic availability.
Do you serve clients outside of Texas?
Absolutely. While we are headquartered in Frisco, we provide enterprise cybersecurity solutions for organizations throughout the entire United States, utilizing cloud-native tools and remote monitoring.
What happens if a threat is detected?
Our Autonomous Response Protocol immediately isolates the affected segment of the network while alerting our SOC team. We then perform a deep-dive forensic analysis to ensure the threat is completely eradicated before restoring full access.
Do you offer security for remote employees across the US?
Yes. We implement secure VPN tunnels and “Zero-Trust” access points that allow your team to work securely from any state, ensuring the integrity of your corporate network remains intact.
